This is an automated archive made by the Lemmit Bot.
The original was posted on /r/programming by /u/No_Plan_3442 on 2026-03-27 10:36:30+00:00.
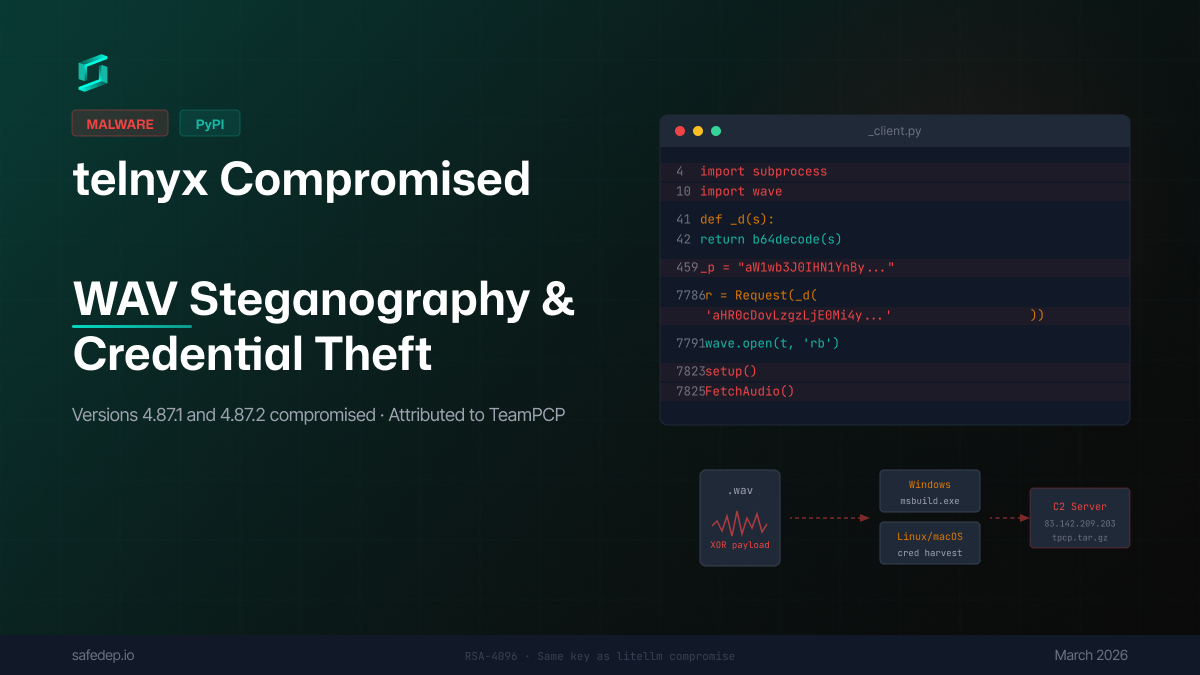
Same actor, same RSA key, same tpcp.tar.gz exfiltration header as the litellm compromise last week.
This time they injected into telnyx/_client.py - triggers on import telnyx, no user interaction needed. New trick: payload is hidden inside WAV audio files using steganography to bypass network inspection.
On Linux/macOS: steals credentials, encrypts with AES-256 + RSA-4096, exfiltrates to their C2. On Windows: drops a persistent binary in the Startup folder named msbuild.exe.
They even pushed a quick 4.87.2 bugfix to fix a casing error that was breaking the Windows path. These folks are paying attention.
Pin to telnyx==4.87.0. Rotate creds if you installed either version.
Full analysis with IoCs here https://safedep.io/malicious-telnyx-pypi-compromise/
“TeamPCP is getting too predictable. Anyone else think it’s time for a more robust vetting process on PyPI?”